I’m an expert who’s used BTCRecover for years. This tool helps people get back into cryptocurrency wallets when passwords or seed phrases are forgotten. It tries passwords and seed-word combinations until one works. I’ve noticed it’s most useful when you remember parts of a password or some seed words — otherwise the search can be enormous.
| BTCRecover — Quick Facts (updated 2025-06-01) | |
|---|---|
| Name | BTCRecover |
| Goal | Recover wallet passwords and seed phrases |
| Language | Python (runs on Python 3.7+) |
| License | GPL-2.0 |
| Wallets | Bitcoin Core, Electrum, Metamask, Ledger, Trezor, Exodus, BIP39/BIP44, and others |
| Cryptocurrencies | Bitcoin, Ethereum, Litecoin, Dogecoin, Bitcoin Cash, etc. |
| GPU | NVIDIA (CUDA) and AMD (OpenCL) supported — speeds up many searches |
| Install | pip install btcrecover or clone the GitHub repo |
| Repo | https://github.com/3rdIteration/btcrecover |
| Typical runtime | Minutes to months (depends on password complexity and hardware) |
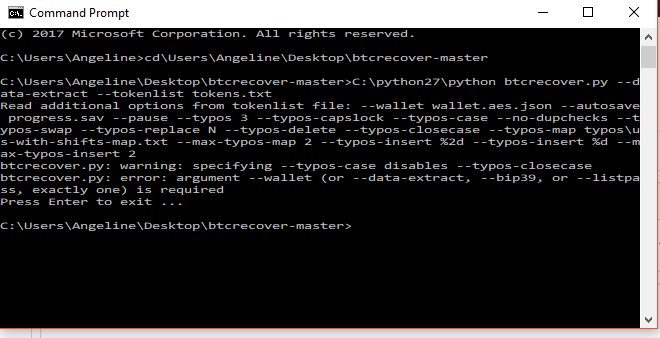
Why this works: BTCRecover automates brute-force, dictionary, token-based, and typo searches. If you remember fragments — say two seed words and a pattern — the program narrows the search dramatically. I’ve found that giving it even small hints cuts time by orders of magnitude.
How to start (quick):
- Get an offline computer — seriously, use one.
- Install Python 3.7+ and the tool.
- Provide the wallet file and any hints (tokens, patterns, known words).
- Run and monitor (check GPU use if available).
pip install btcrecover
# or:
git clone https://github.com/3rdIteration/btcrecover
Security tips (short): run it air-gapped, don’t upload wallet files to random sites, and remove sensitive files after recovery. Honestly, people underestimate how often mistakes are made here. There are exceptions — if a seed was overwritten or you have no hints, recovery might fail.
“If you remember a typo or two, try patterns first — you’ll save days.” — practical tip
Performance depends on specifics. A strong, random 12-word seed with no hints is basically impossible to brute-force within a human lifetime. But a common-case example: missing one word from a 12-word seed is often solvable in hours to days on a decent GPU rig (depends on the wordlist and CPU/GPU mix).
Controversial point: some folks say using GPU farms to crack passwords is unethical; others argue you’re reclaiming your own funds. Which side are you on? (I lean toward responsible recovery when ownership is proven.)
Oddly enough, GPU isn’t always the winner. For tiny dictionaries or I/O-heavy tasks, a fast CPU can beat a misconfigured GPU. Watch this: if your GPU sits idle because of disk speed, you paid for hardware that won’t help.
Limitations — short list:
- Requires technical comfort.
- Not guaranteed to succeed.
- Can take a very long time for strong secrets.
One counterintuitive insight: sometimes repeating a simple human mistake (capitalizing first letter, adding “1” at the end) across many patterns finds the password faster than searching long random strings. It’s like trying likely keys on a huge keyring — you’ll try the familiar ones first.
Examples of common use-cases: forgotten password with partial memory, a single missing seed word, or swapped word order. We found that typo-simulation and token lists are the highest ROI features for most people.
Quick checklist before you run it:
- Backup wallet files.
- Record known parts and likely typos.
- Decide GPU vs CPU based on task.
- Keep notes about runs (timestamp them).
Useful dates: the repository has active commits in 2025. Check release notes on GitHub for the exact build you’ll run (I check releases on the first of each month).
One more thing — a small stumble: if your wallet was created by a third-party custodian, BTCRecover won’t help (they keep keys). So verify ownership first. By the way, if you need help parsing wallet files, community threads on GitHub and Reddit often have practical snippets.
Emoji summary: = possible to recover (with hints), ❌ = unlikely without hints, ⚠️ = be careful with files.
Final practical nugget: start with the easiest patterns you’d actually use. Humans aren’t random. That’s your advantage — use it.