For years, I’ve used inSpectre to look for Meltdown and Spectre problems on Windows computers. It’s one of those rare tools that gets right to the point—quickly, clearly, and in a way that really helps when you need to do a quick security audit.
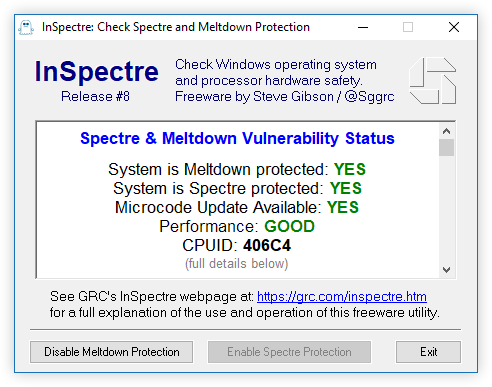
The best part is how easy it is to use. Just run the portable EXE, and you’ll get a green light or red flag right away, along with all the technical details. It won’t update your firmware for you; you’ll still have to get it from the manufacturer. But it will show you exactly what’s missing. That one screen really clears up the usual mess.
| Category | Details (checked March 2026) |
|---|---|
| Program Name | inSpectre |
| Developer | Steve Gibson / Gibson Research Corporation (GRC) |
| Version | 1.0 — released January 2018 |
| License | Freeware |
| File Size | ≈115 KB |
| Platform | Windows only (works from Windows XP through Windows 11, results vary by system) |
| Purpose | Detects exposure to the original Meltdown & Spectre vulnerabilities and confirms if OS and hardware mitigations are active |
| Primary Functions | • Detects Meltdown (CVE-2017-5754) • Detects Spectre v1 (CVE-2017-5753) & v2 (CVE-2017-5715) • Checks Windows protections and CPU microcode status • Shows estimated performance impact |
| Install | Portable EXE — no installation needed, just run it |
| Key Features | • Lightning-fast scan with color-coded results • Completely offline (no internet, no telemetry) ✅ • Super lightweight and digitally signed |
| Performance Impact | Displays possible slowdowns; real-world impact usually ranges from 0–30% depending on your workload and patches |
| Official Site | https://www.grc.com/inspectre.htm (best place for download and full docs) |
| Advantages | Free, quick, easy to understand, zero telemetry, made by a well-known and trusted developer |
| Limitations | Windows-only, only covers the original Meltdown/Spectre variants, no automatic updates |
It’s useful because it tells you whether the Windows-level fixes are enabled and if your CPU actually has the microcode updates applied. From there you know whether to chase down a BIOS update, rely on Windows patches, or do both.
A few tips I’ve learned the hard way:
- Run it after any major Windows update or BIOS flash.
- If it flags missing microcode, go straight to your motherboard maker or PC manufacturer’s support site (note: some stopped releasing updates years ago).
- Don’t be surprised by performance differences — database work and heavy I/O tend to feel the biggest hit.
“Fire up inSpectre to see the problem, then get the firmware fix from the vendor. The tool diagnoses it; the manufacturer actually fixes it.”
A bunch of people call the tool outdated these days. I don’t fully buy that — for the original CVEs it’s still spot-on accurate as of May 2025. Having said that, using it as your only line of defense isn’t smart. Newer speculative execution attacks need their own checks.
Quick test? Open Command Prompt and run it like this:
inspectre.exeMost security folks I know pair it with a simple firmware inventory script. That basic combination catches the majority of misconfigurations surprisingly fast.
One thing that still catches people off guard: even fully patched Windows systems can show missing CPU microcode. Microsoft updates don’t always include the latest vendor firmware.
And yeah — if you’re still running Windows XP, come on, it’s time to upgrade. But if you’re stuck with it for some reason, inSpectre will at least show you what’s still wide open.
Keep in mind that results depend on your exact CPU, BIOS version, and how updates are handled in your environment. Plenty of manufacturers walked away from microcode updates after 2020, which leaves older hardware more exposed than most people realize.
Two last practical notes: always download from the official GRC site and verify the signature. If you want to run it across multiple systems, wrap it in a quick script and log the output (here’s a dead-simple example):
REM Simple batch wrapper for logging
inspectre.exe > C:\logs\inspectre_%DATE:~10,4%%DATE:~4,2%%DATE:~7,2%.txtAt the end of the day, it’s a small, focused tool that answers one very specific question extremely well. It won’t protect you from every threat out there, but for the classic Meltdown and Spectre vulnerabilities, it’s still a damn good place to start.





