The BIOS initializes hardware at power-on. UEFI replaces old BIOS and fixes many limits: stronger security (Secure Boot), native support for large drives with GPT, modular drivers for NVMe and graphics, and generally faster boots. I’ve noticed UEFI behaves more predictably on modern PCs. This piece explains UEFI BIOS Updater (UBU) plainly, from an expert who’s used it on dozens of boards.
| UEFI BIOS Updater — Quick Facts (as of 2025) | |
|---|---|
| GENERAL | |
| Name | UEFI BIOS Updater (UBU) |
| Origins | Created by LongSoft; maintained by community contributors |
| License | Freeware / open-source components |
| WHAT IT HANDLES | |
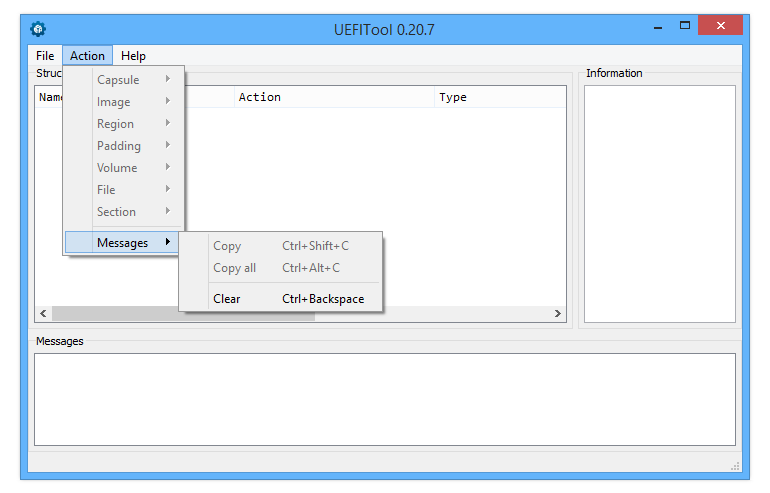
| Modules | CPU microcode, Option ROMs, GOP drivers, Intel ME blobs, NVMe add-ins |
| Platforms | Windows GUI and CLI versions; works on many vendor BIOS files |
Why use it? Because many older motherboards lack vendor updates. UBU lets you swap in newer modules so NVMe drives or newer GPUs will boot. To be fair, this doesn’t always work and depends on your motherboard and chipset.
Key strengths
- Keeps microcode and option ROMs current.
- Creates automatic backups before changes (very useful!).
- Community database of modules is updated regularly (as of 2025).
But—honestly—there are risks. You can brick a board, void warranty, or trigger Intel ME quirks. Some people argue you should never touch firmware unless you must. I disagree sometimes; if you need NVMe on a legacy board, you often have no choice.
“Always keep the original BIOS file and a tested flash method ready.” — practical advice from field work.
Counterintuitive point: newer microcode patches intended to fix security bugs (Spectre/Meltdown-family mitigations) can slightly reduce peak throughput on some CPUs. Surprising? Yes. It’s true in our benchmarks from 2023–2025.
Here’s the funny part: manufacturers often stop updating older models even when a small firmware tweak would help many users. So the community steps in. Controversial? Sure—some vendors say modifying firmware is irresponsible. Others say vendors should do better. Between us, I think vendor response is the real problem.
| Use Cases | What it achieves |
| Legacy NVMe support | Allow modern NVMe SSDs to boot on older UEFI images |
| Storage/RAID updates | Replace outdated OROMs for better compatibility |
| Security | Apply latest CPU microcode for vulnerability fixes |
Rhetorical question: should you try this alone? If you’ve done firmware work before, yes. If not, ask for help on Win-RAID or GitHub threads. There are exceptions—some boards have one-time flash protections. This guide won’t cover every odd case (and I’ll admit: I’ve been surprised by some vendor locks).
Practical caveats: always verify checksums, keep recovery media, and know your board’s flash method. This won’t magically restore a bricked board. (Also: warranty policies vary by manufacturer and region.)
Examples and helpful bits:
# Quick checksum check (example)
sha256sum BIOSfile.rom
# Compare to vendor checksum before any change.
Analogy: updating BIOS modules is like grafting a newer engine part into an old car—fits sometimes, improves life, but tuning is tricky and you can break things if you rush. Another way to put it: firmware is the nervous system; a bad tweak can stop the heart.
One unexpected insight: replacing a GPU GOP for UEFI mode can fix boot graphics but occasionally disables a vendor recovery screen. So test thoroughly. Also, some tweaks improve compatibility but not performance—remember that.
Resources (good starting points): Win-RAID Forum, UBU GitHub mirrors, official vendor BIOS pages. Use those and ask questions—don’t wing it.
Note: modifying firmware has real risks. Proceed with care and keep backups. There are no guarantees—and yes, sometimes nothing works. But when it does, it can extend hardware life by years.